Secure Information Destruction and Computer System Recycling Services for Organizations
In an era where information violations and personal privacy worries are ending up being progressively common, making sure the safe damage of sensitive information has come to be a crucial duty for organizations. This is where specialist safe data destruction and computer system recycling solutions come into play. How specifically does safe and secure information destruction job?
Value of Secure Data Destruction
Secure information damage is of utmost significance for services to shield sensitive information and protect against possible data violations. In today's electronic age, where data is a beneficial possession, organizations have to take positive steps to make certain that their private data is firmly destroyed when it is no more needed. Failing to do so can subject businesses to considerable risks, consisting of financial loss, reputational damages, and lawful ramifications.
When sensitive information is not properly ruined, it can drop right into the wrong hands, causing information breaches and identity burglary. Cybercriminals are frequently seeking chances to manipulate weak security steps and obtain unapproved access to important details. By carrying out secure data damage techniques, organizations can mitigate these risks and protect their delicate information.
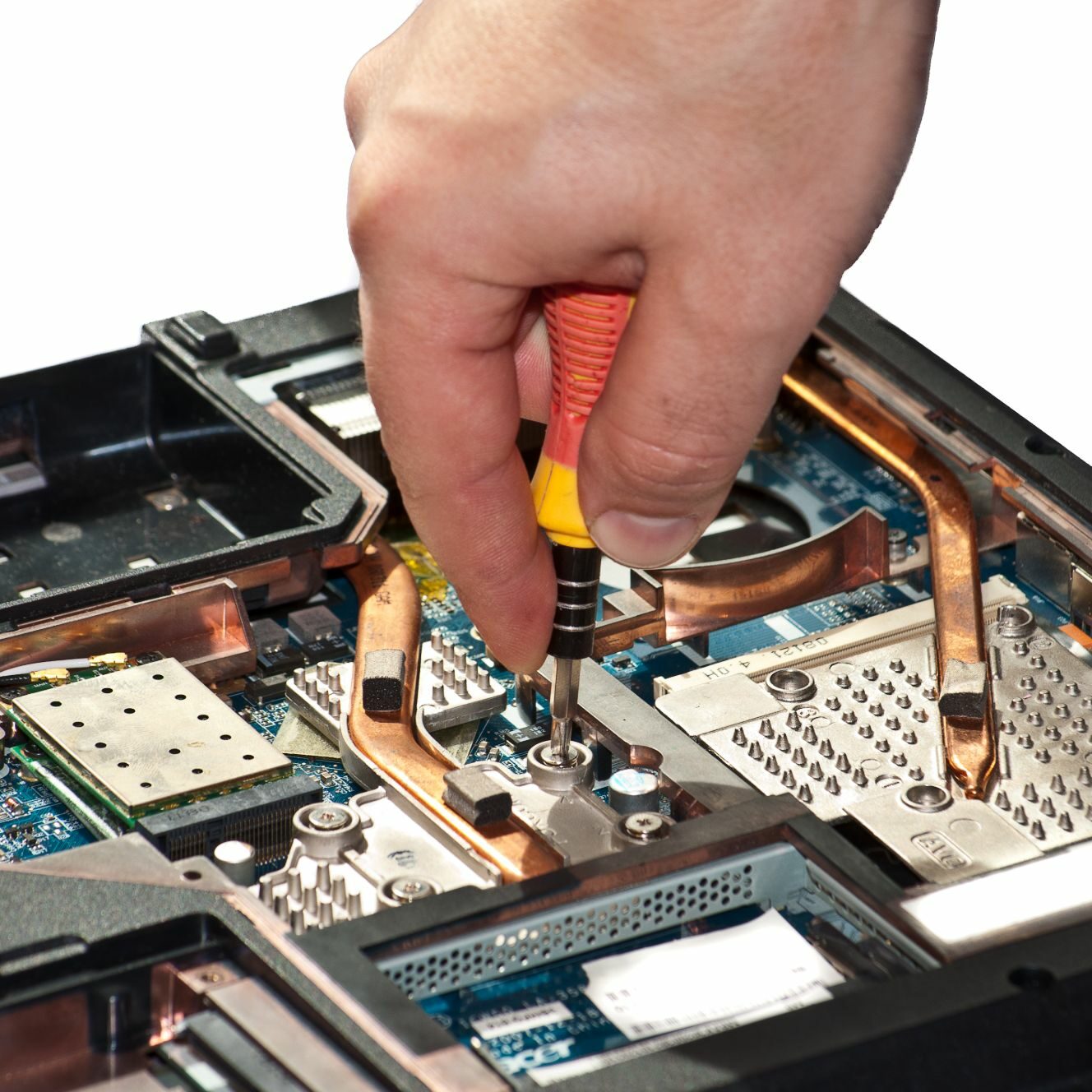
Safe and secure information devastation involves the complete and irreversible damage of all data stored on digital tools, such as tough drives, solid-state drives, and mobile devices. This process guarantees that the data can not be recuperated or accessed by unauthorized individuals. It is vital to make use of trusted information devastation approaches, such as degaussing, shredding, or information cleaning utilizing specialized software program, to make sure the total elimination of data.
Additionally, protected data destruction is not only important for protecting delicate consumer info however also for regulatory conformity. Several markets, such as health care and finance, have strict information security policies that require companies to safely get rid of sensitive information (computer recycling). Failing to adhere to these regulations can cause serious penalties and lawful repercussions
Advantages of Expert Computer Recycling
As organizations prioritize secure information destruction, they can additionally enjoy the advantages of expert computer reusing services. Expert computer system reusing deals various advantages for organizations seeking to deal with their old or obsolete equipment in a environmentally pleasant and liable way.
Among the primary advantages of professional computer system recycling is the guarantee that sensitive information is completely and safely erased from all gadgets. This removes the risk of information violations and guarantees conformity with data security laws. By utilizing specialist solutions, companies can have satisfaction recognizing that their data is being managed and damaged correctly.
Along with information security, expert computer system recycling additionally helps companies lessen their effect on the environment. Electronic waste, or e-waste, consists of unsafe substances such as mercury, lead, and cadmium, which can leach right into the dirt and water otherwise disposed of correctly. Professional recyclers have the knowledge and know-how to securely get rid of and get rid of of these dangerous materials, minimizing the environmental impact of electronic waste.
Additionally, expert computer recycling promotes sustainability by helping with the reuse and healing of important resources. Recycling old computers and IT tools permits for the removal of beneficial steels and elements, which can then be utilized in the manufacturing of new tools - computer recycling. This lowers the demand for raw products and energy usage, adding to a more circular and lasting economic situation
Actions to Guarantee Data Security Throughout Damage
To guarantee the utmost information safety during the devastation procedure, companies must adhere to a collection of precise actions. These actions are vital to prevent any kind of prospective data violations and safeguard sensitive info from coming under the wrong hands. The primary step is to assess the information that needs to be damaged. This entails determining all the storage tools and making sure that no information is neglected. When the supply is full, the next action is to choose the ideal technique of devastation. Choices consist of physical destruction, such as shredding or squashing, or degaussing and overwriting for magnetic media. The chosen technique needs to be compliant with sector standards and guidelines.
After picking the destruction method, it is vital to entrust the task to a certified and reputable information devastation solution carrier. These service providers have the experience and customized equipment to execute the destruction process securely. It is very important to establish a chain of wardship and get a certification of destruction as evidence that the information has actually been damaged properly.
Additionally, businesses ought to also consider implementing data encryption and secure disposal practices within their organization. Securing delicate information makes sure that even if it falls under the incorrect hands, it continues to be pointless and unreadable. Protected disposal practices involve firmly getting rid of information from storage devices prior to deactivating or repurposing them.

Eco-Friendly Techniques for Computer System Disposal
In accordance with liable information devastation and computer system recycling methods, services must likewise prioritize using environmentally friendly techniques when getting rid of click for source their computers. With the enhancing issue for environmental sustainability, it is crucial that businesses take on actions that decrease the effect of computer disposal on the environment. Among one of the most effective ways to attain this is with appropriate recycling procedures.
When it pertains to environment-friendly computer disposal, reusing is the trick. Reusing permits the recuperation and reuse of valuable materials, reducing the demand for source extraction and reducing waste. By recycling computer systems, organizations can help preserve all-natural resources, minimize greenhouse gas discharges, and protect against harmful substances from going into the setting.
To make sure environment-friendly computer system disposal, businesses should partner with qualified recycling business that stick to stringent environmental requirements. These firms have the expertise and infrastructure to securely take apart and recycle computers, drawing out beneficial parts such as steels, plastics, and glass for reuse. They also make sure that dangerous products, such as lead, mercury, and brominated fire retardants, are effectively managed and dealt with in an ecologically accountable way.
Along with recycling, businesses can additionally think about contributing their computers to philanthropic companies or colleges. This not only prolongs the life-span of the devices yet additionally provides access to technology for those that might not have the means to afford it. However, it is essential to guarantee that the donated computer systems are in important source excellent functioning condition and have been effectively wiped of any type of sensitive data.

Picking the Right Secure Information Damage Provider
When selecting a safe data destruction carrier, services ought to focus on companies that have a proven record of implementing robust data defense steps. It is crucial for organizations to guarantee that their delicate information is taken care of and destroyed firmly to prevent any potential information breaches or unapproved access. Selecting the appropriate information damage carrier is of utmost significance.
One vital factor to take into consideration when picking a provider is their certification and conformity with sector criteria. Look for providers that comply with commonly recognized standards such as ISO 27001, which makes certain the application of effective information protection administration systems. Additionally, qualifications like NAID AAA (National Association for Information Devastation) supply assurance that the carrier complies with best techniques in data devastation.

In addition, services should assess the company's data taking care of procedures, consisting of the chain of custodianship and transportation procedures. Ensure that the supplier follows stringent protocols for gathering, transporting, and keeping the information securely throughout the damage procedure.
Lastly, think about the provider's credibility and customer reviews. Research study the firm's background, checked out testimonials, great site and request recommendations from previous customers. This will certainly help evaluate the supplier's degree of professionalism and reliability, client, and integrity satisfaction.
Conclusion
To conclude, protected data destruction and professional computer recycling services are essential for businesses to protect sensitive information and abide by ecological laws. By adhering to correct actions to make sure data safety and security during destruction and making use of green disposal approaches, organizations can secure their data and add to a lasting future. It is critical for businesses to pick the ideal safe data damage carrier to make certain the highest degree of safety and security and conformity.
Safe and secure data destruction is of utmost relevance for services to safeguard sensitive details and avoid potential information breaches. By applying safe data devastation practices, organizations can alleviate these risks and guard their sensitive information.
Protected information damage entails the permanent and complete damage of all data kept on digital gadgets, such as tough drives, solid-state drives, and mobile devices. It is critical to utilize reliable data devastation methods, such as degaussing, shredding, or information wiping using specialized software program, to guarantee the full eradication of information.
When picking a protected information devastation company, organizations should prioritize firms that have a proven track record of carrying out durable data security procedures.

:max_bytes(150000):strip_icc()/GettyImages-939606046-9e72bdb3e2af4b5db49ff63925f4f6b3.jpg)





